The war between the United States, Israel, and Iran — which began with coordinated U.S.-Israeli airstrikes on February 28, 2026 — has brought an unprecedented homeland dimension to American life. For the first time in decades, U.S. intelligence agencies are actively tracking the possibility of organized, foreign-directed attacks on American soil, and the threat vectors extend well beyond traditional military targets.
This article breaks down what we know, what the FBI and DHS are warning about, and what it means for Americans living in connected, smart homes.
The FBI Alert: Iranian Drones Off California’s Coast
In late February 2026 — timed precisely to the beginning of U.S.-Israeli strikes against Iran — the FBI distributed an alert to California law enforcement agencies warning of a previously assessed Iranian aspiration to conduct attacks against U.S. targets.
What the Alert Said:
“As of early February 2026, Iran allegedly aspired to conduct a surprise attack using unmanned aerial vehicles (UAVs) from an unidentified vessel off the coast of the United States, specifically against unspecified targets in California, in the event that the U.S. conducted strikes against Iran.”
The FBI memo acknowledged significant uncertainty, noting it had “no information on the timing, method, target, or perpetrators” of the alleged planned attack.
California Governor Gavin Newsom followed up by stating there was no “imminent threat” to the state, and multiple senior U.S. and state law enforcement officials told reporters there was “no credible intelligence” underpinning the bulletin.
Why the Alert Still Matters:
Despite the lack of confirmed credibility, the alert represents something significant: U.S. intelligence agencies assessed Iranian drone deployment against California as a threat serious enough to formally warn law enforcement — a standard not typically met by aspirational threat reporting alone.
The Range Problem:
Security analysts quickly noted a major practical barrier: San Francisco is approximately 7,100 miles from Iran, and Los Angeles approximately 7,500 miles. Iran’s longest-range drone systems — the Shahed-136 and its variants — have a maximum range of approximately 1,200 miles. A sea-launched drone operation would require a vessel covertly positioned off the U.S. Pacific coast, a significant logistical challenge that U.S. naval surveillance would likely detect.
A senior law enforcement official also noted that the 12-day bombardment of Iranian infrastructure by U.S. and Israeli forces has “severely degraded Iran’s capabilities to carry out such an attack.”
The DHS Warning: Encrypted Messages and Sleeper Assets
More alarming than the drone threat — at least from an intelligence standpoint — is a separate DHS and FBI alert concerning encrypted communications intercepted shortly after the death of Supreme Leader Ayatollah Ali Khamenei on March 1, 2026.
What Intelligence Agencies Found:
U.S. intelligence agencies intercepted encrypted communications believed to have originated from Iran that may serve as “an operational trigger” for “sleeper assets” outside the country. Law enforcement agencies were instructed to:
- Increase monitoring of suspicious radio-frequency activity
- Heighten surveillance of known or suspected Iranian-linked individuals
- Boost physical security posture at federal and critical infrastructure sites
DHS emphasized that there is “no operational threat tied to a specific location” — but the intercept was serious enough to generate a formal multi-agency alert.
American Counterterrorism’s Assessment:
U.S. counterterrorism agencies are now actively monitoring suspected sleeper cells on U.S. soil. Federal and local law enforcement have boosted security in major U.S. cities. Public reporting indicates “no confirmed evidence of a large-scale Iranian sleeper-cell network currently operating inside the United States,” though intelligence agencies consider the possibility credible enough to act on.
The DHS Threat Landscape:
The Department of Homeland Security’s current threat assessment covers several distinct vectors:
- Iran-aligned hacktivists — Low-level cyber attacks such as website defacements and distributed denial-of-service (DDoS) attacks against government and corporate websites
- Lone wolf violence — DHS warns of heightened risk that U.S.-based violent extremists or hate crime perpetrators may target entities perceived as Jewish, pro-Israel, or linked to the U.S. government or military
- Sleeper cell activation — Coordinated action by long-dormant Iranian intelligence assets in response to the Khamenei death and subsequent encrypted trigger communications
- Smart infrastructure targeting — State-sponsored and hacktivist actors targeting connected public infrastructure including utilities, transportation systems, and communications networks
What This Means for Smart Home Owners
At first glance, the connection between an Iranian military threat and your smart doorbell or home automation hub may seem abstract. But in the context of a nation-state hybrid warfare campaign — one that blends physical attacks, cyber operations, and information warfare — connected devices in American homes become part of a broader attack surface.
1. Your Smart Devices Are Part of National Infrastructure
Modern smart home ecosystems are deeply integrated with national infrastructure systems. Your smart thermostat routes through cloud servers. Your IP camera connects to storage platforms. Your smart speaker processes queries through data centers. When nation-state actors target ISPs, CDNs, or cloud infrastructure — as Iranian APT groups have been documented doing — the downstream effect reaches consumer devices.
The implication: A successful attack on a major U.S. cloud provider or ISP isn’t just a corporate breach — it affects the 150+ million American households with smart home devices.
2. Drone Threats and Smart Home Sensors
The FBI’s concern about sea-launched Iranian drones off the California coast introduces a scenario most smart home security systems are not designed for: an aerial physical threat.
What smart home devices could be relevant:
- Outdoor security cameras — Most consumer IP cameras lack upward-facing fields of view designed to detect aerial objects
- Smart doorbells — Ring, Nest, and similar devices typically cover ground-level entry points, not airspace
- Weather stations and environmental sensors — These devices can detect unusual atmospheric signatures but are rarely integrated into emergency alert systems
- Smart speakers and alert systems — Alexa Guard and similar products are designed for interior intrusion detection, not external aerial threats
The takeaway: Consumer smart home security is fundamentally not designed as a counter-drone or aerial surveillance system. However, maintaining fully operational outdoor cameras with motion alerts, cloud backup, and uptime monitoring ensures that if an incident occurs near your property, you have documentary record.
3. The Insider Access Threat: Your Network Is Your Vulnerability
The most realistic smart home threat in the current Iranian threat environment is not a drone — it’s a cyber intrusion. Specifically:
Botnet Recruitment: Iranian and Iranian-aligned threat actors have historically recruited large botnets from compromised consumer IoT devices to conduct DDoS attacks against U.S. government and corporate targets. Your router, smart camera, or NVR could be conscripted into an attack without your knowledge.
Credential Harvesting: Infostealer malware — the same class of tools used in the concurrent attack against Stryker Corporation — targets browser-stored credentials for everything from banking to smart home management platforms. A compromised laptop or phone with your Nest or Ring credentials gives an attacker access to your home’s sensor network.
Reconnaissance Value: Smart home devices that monitor motion, occupancy, and environmental conditions can provide adversarial intelligence about patterns of life. For individuals in sensitive government, military, or critical infrastructure roles, this data has significant operational security (OPSEC) implications.
Practical Smart Home Security Steps During Elevated Threat Conditions
The DHS threat posture as of March 12, 2026 is elevated but not panic-inducing for most households. The following steps reflect prudent security hygiene calibrated to the current environment:
Immediately:
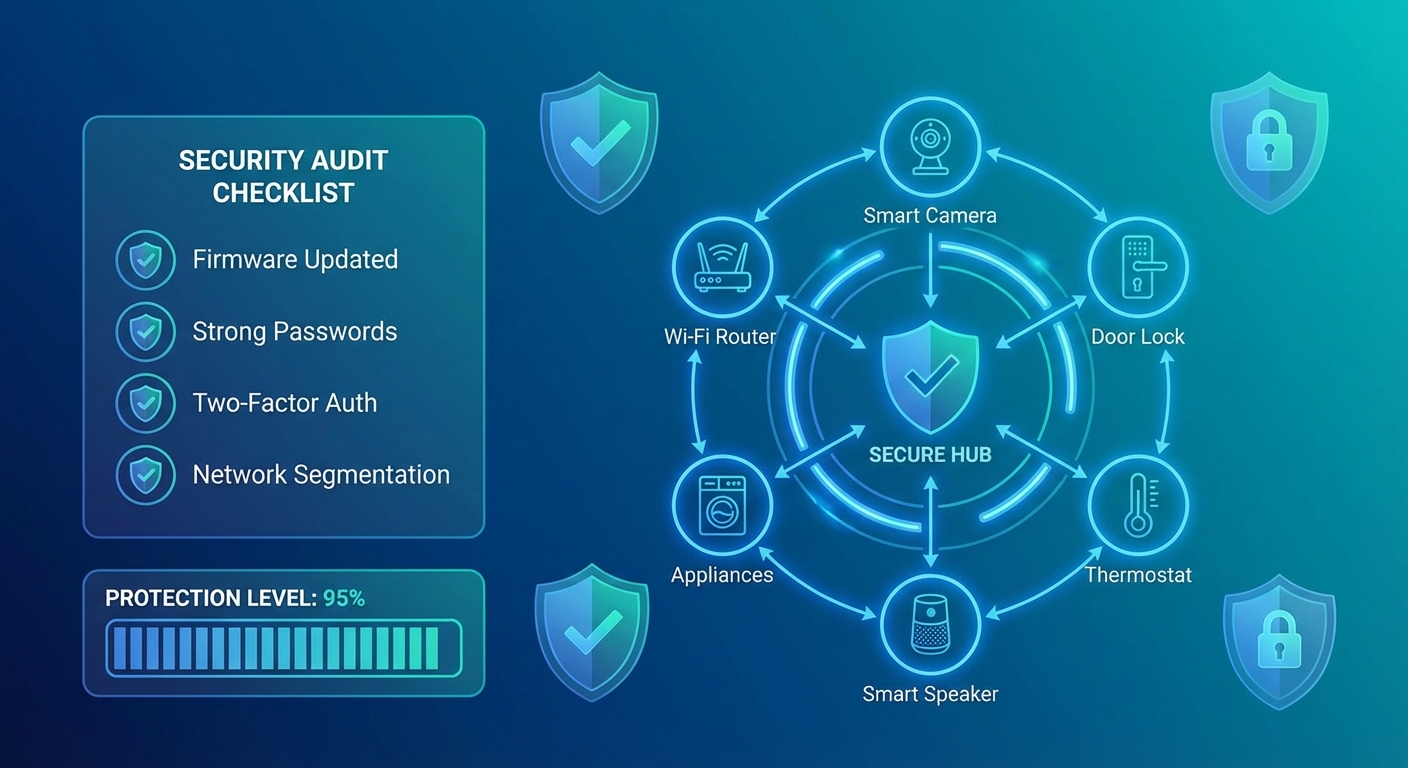
1. Update all smart home device firmware Iranian and Iranian-linked threat actors target known, unpatched vulnerabilities. Every smart device on your network — camera, thermostat, hub, router — should be running its latest firmware. Enable automatic updates wherever possible.
2. Change default credentials on all devices Default usernames and passwords on IoT devices are the single most exploited entry point for botnet recruitment. Every device should have a unique, strong password.
3. Segment your IoT network Create a separate Wi-Fi network (VLAN or guest network) for smart home devices, keeping them isolated from computers and phones where sensitive data is stored. Most modern routers support this natively.
4. Review app permissions and cloud access Audit which smart home apps have access to your device network. Revoke permissions for apps you no longer actively use. Disable remote access features on devices that don’t require them.
This Week:
5. Enable two-factor authentication everywhere Your smart home platform accounts (Google Home, Apple HomeKit, Amazon Alexa, Samsung SmartThings) should all have two-factor authentication enabled. If an attacker steals your password via infostealer malware, 2FA is the last line of defense before they access your home’s sensor network.
6. Review your router’s DNS settings Consider switching to a secure DNS provider (Cloudflare 1.1.1.1 or similar) that blocks known malicious domains. Several Iranian APT command-and-control servers operate through DNS-based communication — a protective DNS resolver adds a meaningful layer of defense.
7. Check for unfamiliar devices on your network Log into your router’s admin interface and review connected devices. Iranian botnet operators often compromise IoT devices silently; an unfamiliar device on your network should be investigated immediately.
8. Disable UPnP on your router Universal Plug and Play (UPnP) automatically opens ports for devices requesting them — a feature widely exploited by malware to establish external access. Disable it unless you have a specific need.
For High-Risk Individuals:
If you work in government, defense, finance, healthcare, or critical infrastructure, the threat calculus for your smart home is meaningfully higher. Consider:
- Eliminating always-on microphone devices (smart speakers) from rooms where sensitive conversations occur
- Reviewing whether smart home devices can observe work materials — cameras with views of computer screens, documents, or whiteboards
- Consulting your organization’s security team about what smart home devices are permissible given your security clearance or role
The Bigger Picture: Hybrid Warfare Has Reached American Homes
What’s unfolding in March 2026 is a textbook hybrid warfare campaign — one that combines kinetic military action, cyber operations, information warfare, and the activation of pre-positioned human assets. The Iranian strategy is not simply to win a military exchange with the United States; it is to impose costs broad enough and diffuse enough that the American public feels the consequences of the conflict.
That calculus includes making Americans feel less safe in their own neighborhoods — and the FBI drone alert, whatever its ultimate credibility, serves exactly that function. The psychological effect of an FBI warning to California law enforcement about Iranian drones is significant regardless of whether a single drone is ever launched.
Smart home technology — the cameras, sensors, and connected devices Americans use to feel safe in their homes — sits at the intersection of personal security and national security in a way it never has before. Understanding that intersection, and taking the straightforward steps to harden your home network, is the most practical response available to private citizens navigating the first genuinely homeland-proximate conflict of the networked era.
Stay informed. Secure your network. And check back with Secure IoT House for ongoing coverage of the intersection between home technology and national security.
Sources: ABC News, CNN, FBI bulletins via Mercury News, Washington Times, Council on Foreign Relations, Department of Homeland Security, CISA